Featured
Table of Contents
Openvpn Or Wireguard: Which Protocol Is Better?
It is presently under heavy advancement, however already it may be considered the most safe, simplest to use, and most basic VPN option in the industry. Wire, Guard intends to be as simple to configure and release as SSH. A VPN connection is made merely by exchanging extremely easy public secrets precisely like exchanging SSH keys and all the rest is transparently handled by Wire, Guard.
Wire, Guard provides an incredibly fundamental yet effective interface. Wire, Guard has actually been developed with ease-of-implementation and simplicity in mind.
, which goes into more detail on the procedure, cryptography, and principles.

This interface acts as a tunnel user interface. Wire, Guard associates tunnel IP addresses with public secrets and remote endpoints. When the interface sends a package to a peer, it does the following: This package is implied for 192. 168.30. 8. Which peer is that? Let me look ... Okay, it's for peer ABCDEFGH.
What Is Wireguard?
If not, drop it. Behind the scenes there is much taking place to offer proper personal privacy, credibility, and best forward secrecy, using advanced cryptography. At the heart of Wire, Guard is a concept called Cryptokey Routing, which works by associating public keys with a list of tunnel IP addresses that are allowed inside the tunnel (what is wireguard protocol and how does it work?).
Each peer has a public secret. Public keys are short and basic, and are utilized by peers to confirm each other. They can be circulated for use in setup files by any out-of-band technique, comparable to how one might send their SSH public secret to a buddy for access to a shell server.
69:51820 Allowed, IPs = 0. 0.0. 0/0 In the server configuration, each peer (a client) will be able to send out packets to the network user interface with a source IP matching his corresponding list of enabled IPs. When a packet is gotten by the server from peer g, N65Bk, IK ..., after being decrypted and authenticated, if its source IP is 10.
230, then it's enabled onto the interface; otherwise it's dropped. In the server setup, when the network interface wishes to send a packet to a peer (a client), it looks at that package's destination IP and compares it to each peer's list of enabled IPs to see which peer to send it to - what is wireguard protocol and how does it work?.
Openvpn Or Wireguard Vpn

10.10. 230, it will encrypt it utilizing the general public key of peer g, N65Bk, IK ..., and then send it to that peer's newest Web endpoint. In the client configuration, its single peer (the server) will be able to send out packets to the network interface with any source IP (because 0.
0/0 is a wildcard). For example, when a packet is received from peer HIgo9x, Nz ..., if it decrypts and confirms correctly, with any source IP, then it's allowed onto the user interface; otherwise it's dropped. In the client setup, when the network interface wants to send out a package to its single peer (the server), it will secure packages for the single peer with any destination IP address (given that 0.
0/0 is a wildcard). If the network interface is asked to send out a package with any location IP, it will secure it using the public secret of the single peer HIgo9x, Nz ..., and then send it to the single peer's most recent Web endpoint. Simply put, when sending packets, the list of allowed IPs acts as a sort of routing table, and when getting packages, the list of allowed IPs behaves as a sort of gain access to control list.
Wire, Guard is fully capable of encapsulating one inside the other if necessary. Due to the fact that all packets sent on the Wire, Guard interface are secured and verified, and due to the fact that there is such a tight coupling in between the identity of a peer and the permitted IP address of a peer, system administrators do not require complex firewall software extensions, such as in the case of IPsec, however rather they can just match on "is it from this IP?
Wireguard Protocol ?️ - Free Vpn

The client configuration contains an initial endpoint of its single peer (the server), so that it knows where to send out encrypted data prior to it has actually gotten encrypted information. The server configuration doesn't have any preliminary endpoints of its peers (the customers). This is because the server finds the endpoint of its peers by analyzing from where correctly authenticated data stems.
We likewise go over advancement jobs there and prepare the future of the job.

Do not send non-security-related concerns to this e-mail alias. Do not send security-related problems to various email addresses.
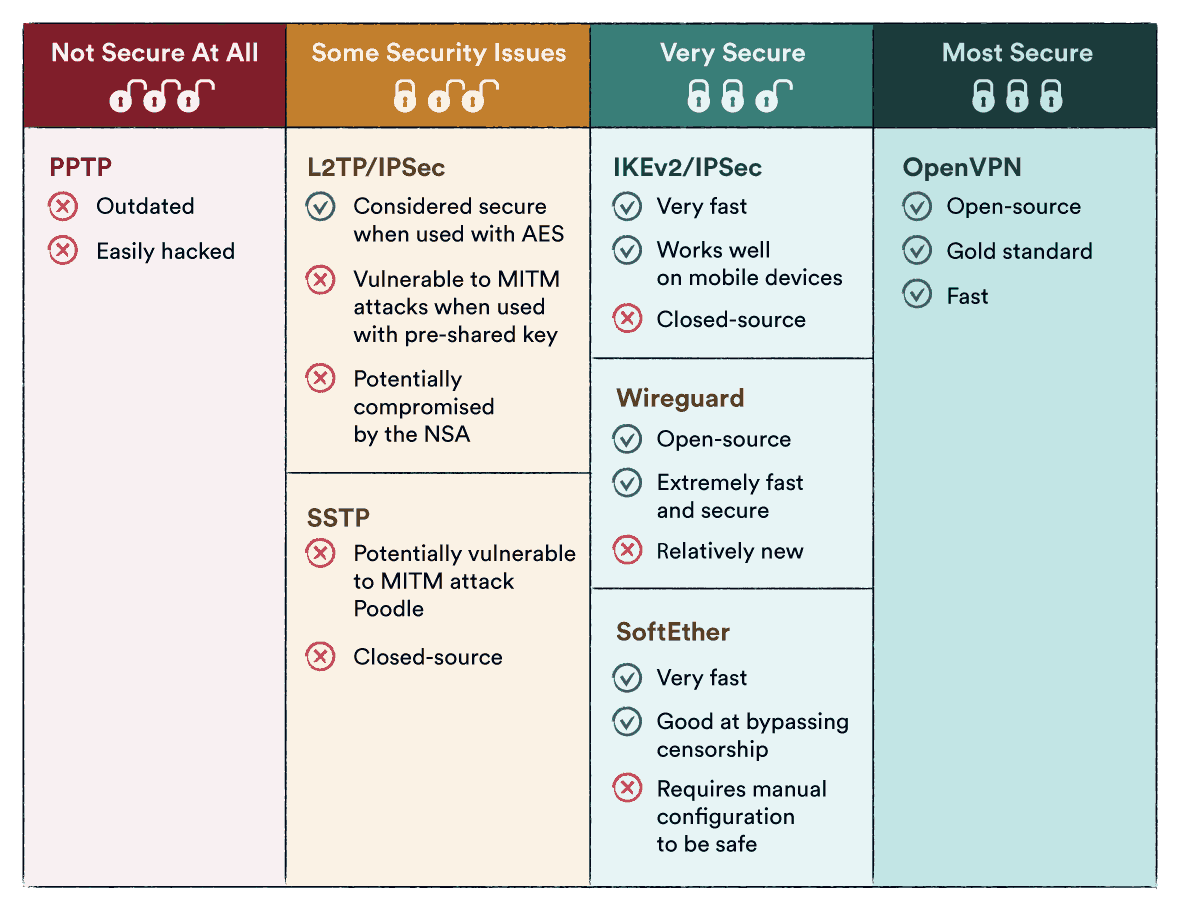
Wire, Guard is much faster than Open, VPN. It consumes 15% less information, handles network modifications better, and appears to be protected. Open, VPN has actually been attempted and evaluated, is more privacy-friendly, and is supported by a bigger number of VPNs.
How To Set Up Wireguard On Debian 11
We may receive payment from the products and services discussed in this story, however the opinions are the author's own. Settlement might affect where offers appear. We have not included all available products or offers. Discover more about how we earn money and our editorial policies. Today, virtual private networks (VPNs) have removed, getting appeal with those searching for extra security, privacy, and flexibility.
In this post Wire, Guard is a new, open-source VPN procedure designed with cutting edge cryptography, which is the practice of coding delicate details so just the desired receivers can analyze its significance. Designer Jason A.
Working with Wire, Guard couldn't be easier. Wire, Guard keeps it easy by running with fewer than 4,000 lines of code compared to older VPN procedures that normally use thousands more.
Latest Posts
Best Vpns For Remote Workers & Freelancers In 2023
Nordvpn: Vpn Fast & Secure 4+ - App Store
The Best Vpns For Small Business 2023 - All About Cookies